Post by Noel on Nov 13, 2016 11:57:13 GMT -6
Any ongoing update strategy involving determining whether to trust Microsoft becomes a study in weighing unknown risks. We can't know what's happening inside Redmond - though we can guess based on evidence and experience.
It should not be like this, but it is. Microsoft has decided that for them, the more unknown their motivations are the better.
To me that implies they are no longer as confident in their own work as they once were. And worse. I really never feel I know enough to make a decision, so it's always a bit uncomfortable - and that's why backups are good to have. Knowing you can - with a suitable investment in time - revert an entire system means that you still have control. Worst case: The system goes to hell after updates, you revert it, continue on and swear off further updates forever.
There is also a subtle undertone emerging more recently having to do with this "cumulative" update business from Microsoft... I believe that Microsoft wants to only deliver blocks of updates at once says that they're not putting the effort into making sure updates stand on their own, i.e., respect well-defined boundaries. It may not be about Microsoft asserting control, though that's no doubt a motivation of theirs. THAT I can counter with my Windows expertise.
All that being brought to light, it remains important to understand available updates and to decide whether to trust Microsoft not to bork your system after the update - vs., it being borked by an unmitigated attack or even just by falling out of date and becoming incapable of communicating or running programs properly.
I look at the potential mechanics of attacks supposedly blocked by each update, and at what functionality the update is supposed to improve. In my own case because of security layers I have put in place I am well protected against running badware from unknown places online, and I'm not moved by "OMG, zero day!" FUD, so I tend to concentrate on functionality improvements. But I'm not so naïve to think I'm 100% protected.
An example of a functionality fix is that there is a current update (having become available in the last few months) that improves the Diffie-Hellman key exchange process. I won't go into detail, but if two parties are preparing to do secure communications, it's important that they use compatible algorithms to do so. Thus the Diffie-Hellman update is one that has to be considered. And lo and behold it will require a reboot. So much for seeing 71 days uptime.
If one considers one part of an update set worth having, one has to make an active determination whether to take ALL the updates, or one runs the risk of having a fragmented system, in which not all the parts are at equal levels of support and maybe becomes unstable.
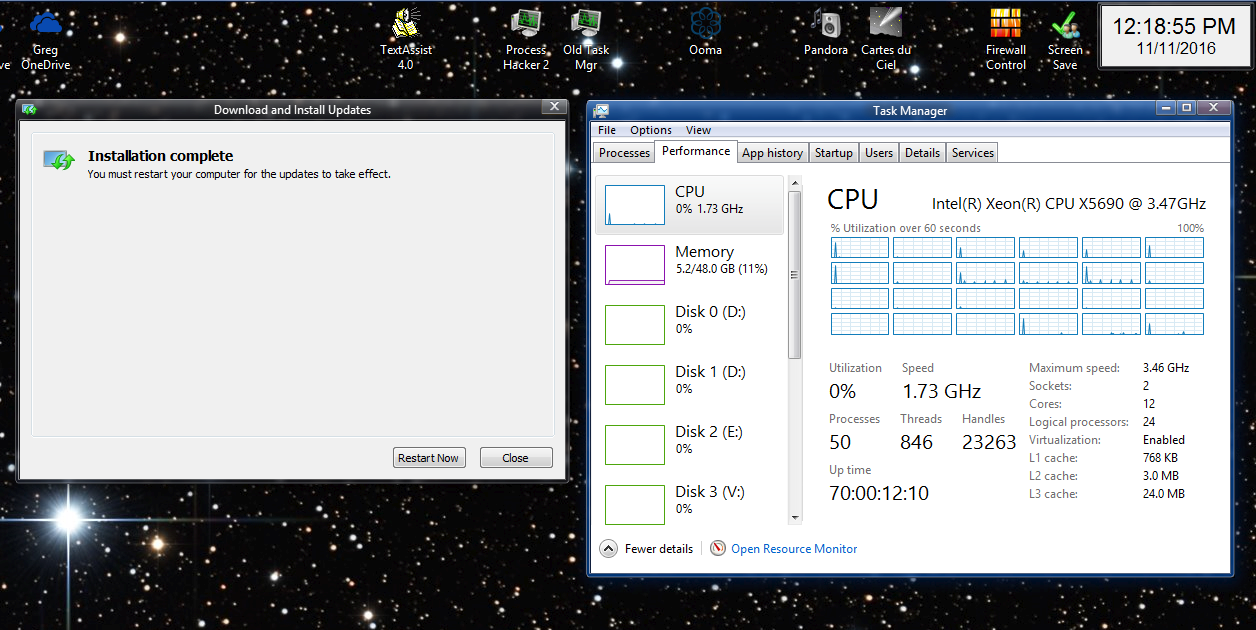
After almost 4 months of "going cold turkey" from taking updates of any kind on my main workstation, running Win 8.1, with the most recent run on a single bootup going 70+ days, I carefully vetted all the updates available.
The number of available updates was significant but not overwhelming. It took me a couple of days of on and off work to get through the list, and in the end I still had to make a judgment about whether to trust Microsoft not to make my system less usable vs. the risks in falling behind w/regard to secure communications.
I even evaluated the "full rollup" that Microsoft has prepared, KB3197874 - "November, 2016 Security Monthly Quality Rollup for Windows 8.1 for x64-based Systems". In light of an "all or nothing" Microsoft that may be reaching a condition where they cannot deliver modular updates, if one were to put ANY in, installing ALL of them - including this one - is probably worth considering. It is touted to bring additional telemetry in, but again I feel I can completely counter additional snooping with my expertise. I maintain complete control over what runs and who it can talk to.
It's still a bit early for anecdotal information about the latest updates borking other people's systems to have made it to the web, so I updated a test VM first, then ran it through the wringer. Restoring a VM snapshot is trivial, so the risk is minimal. It's NICE to have a throwaway system to test with.
The VM hung together, with no obvious degradations or downsides. The only thing I noticed were that a couple of scheduled tasks had gotten changed back from "Disabled" to "Enabled", could only be disabled again via a Task Scheduler run with SYSTEM credentials. In my book that's a good sign that they NEED to be disabled.
Given the apparent good result from my VM, which is set up a lot like my host system workstation, I decided to go ahead and carefully apply the updates to the workstation. I always have up-to-date system image backups (the backup process runs every night) and file backups (likewise), so I made sure my System Recovery USB stick was current then proceeded...
First I put in all the Office 2010 updates (none of which required a reboot), and tested Office. It seems undamaged.
Then I put in the rest of the updates in via Windows Update (which is NEVER allowed to run on its own; I have to reconfigure my firewall and start the Windows Update service in order to request updates).
The total download was some hundreds of megabytes, but proceeded quickly and requested reboot, as expected.
Afterward the system seemed to boot up fine, and I began to look things over in the obvious places to see whether they had changed anything I didn't want changed.
I run a script every night on a schedule that gathers a lot of information - such as what services are set which ways, what scheduled tasks there are and whether they're enabled, what updates are installed, lists bootup parameters, etc., so I ran the script manually and checked for changes using a side by side view in Beyond Compare (fantastic tool). What that told me was the following:
- The BITS service has been changed to AUTO_START (DELAYED) from DEMAND_START
- A new service, DiagTrack, has been added and set to AUTO_START
- A new list of updates are listed as installed (and notably no old ones have been removed)
What I chose to do about the above is as follows:
- Change BITS back to DEMAND_START
- Disable the DiagTrack (telemetry) service. I haven't seen any attempts to send data anywhere new.
- While at it, because I've been reading elsehwhere about Microsoft re-enabling the Windows Update service, I also Disabled all the scheduled tasks in the \Microsoft\Windows\WindowsUpdate\ section.
- I also disabled the Skype Update service just for good measure.
I ran Passmark PerformnceTest benchmarking software, as I always do after any system update, and it didn't indicate any strong reduction in performance. The overall result was about the same as the last run.
The only anomaly I've noticed so far is:
- The first time I ran Visual Studio 2015 after the update it popped up a message to the effect of "an add-in failed", and none of the fonts would show. Closing VS2015 and re-opening it cleared the problem and I haven't seen another problem since.
So... Bottom line: I've once again braved the waters and brought my Win 8.1 system up to date. It seems to be no worse for wear. So far it's been stable in 2 days of normal use.
-Noel







 so the game is ON as far as i'm concerned.
so the game is ON as far as i'm concerned. Hide that mo fo if you don't wanna be a CEIPer
Hide that mo fo if you don't wanna be a CEIPer



